Features:
A cybersecurity installfest for journalists
Lessons from the Hacks/Hackers NYC hands-on event
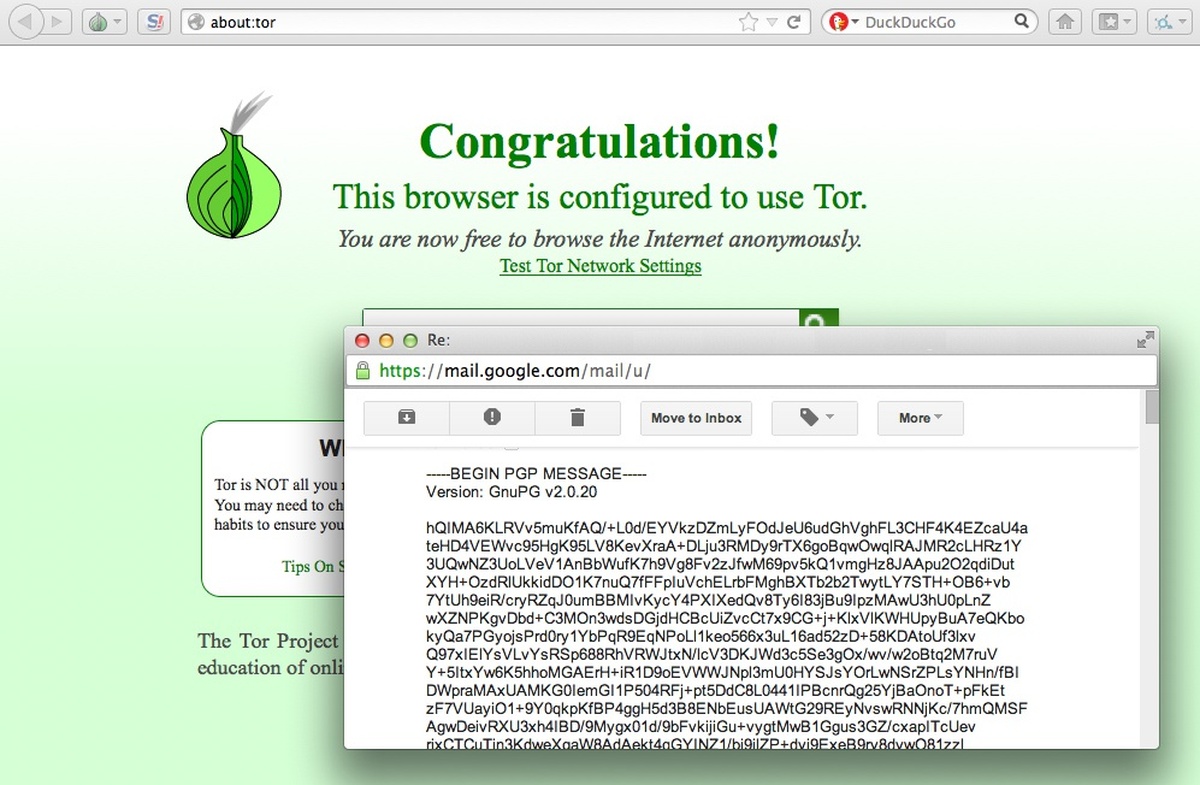
Participants in the installfest learned how to install Tor. (Image: courtesy Mike Tigas)
Hacks/Hackers NYC hosted an “Encryption and Operational Security for Journalists” meetup not too long ago. Unlike most security-for-journalists talks, we told attendees to pack their laptops and get ready for an “installfest,” too. About 70 people signed up to learn more about how cybersecurity affects all journalists — even those who don’t cover privacy and national security issues. More importantly, attendees learned how to install a few tools that can help.
An Opening Conversation
We started off with a presentation by Jennifer Valentino-DeVries, reporter at the Wall Street Journal. The presentation introduced the tools and focused on why journalists should care right now. Jenna Telesca, a journalist who attended the event, summarized some of the key points of the conversation:
Only suckers leave their doors unlocked.
Which is why at Monday’s Hack Hackers class Jennifer Valentino-DeVries likened using encryption tools to locking your house. Sure, someone motivated can get in, but it’s harder.
“What these tools do is minimize your attack surface,” she said.
And while your journalism beat may not make it necessary for you to communicate securely with sources, it’s really hard to learn how to when the need presents itself. So, it’s good to be prepared.
To me, the most important point that Valentino-DeVries made was that people who use encryption can be unfairly seen as having something to hide. The more journalists participate, the more encryption can be seen as just a normal part of doing business and communicating with sources.
The Installfest
The remaining hour-and-a-half of the evening was spent on what we gleefully called an “installfest.”
Before the event, we told attendees to check out this page ahead of time and download the tools listed before arriving. (To my surprise, nearly all of the 70 attendees had done this.) As people arrived, we also attempted to get people grouped together by operating system. By my count, we had about 2/3 Mac OS X users and 1/3 Windows users. (We also had a handful of Linux folks.)
How it Went Down
In the planning stages, we knew that we wouldn’t get a chance to cover a lot of ground in the short amount of time. So we decided to keep the installfest limited to a few tools that are either super simple or super important when it comes to communicating securely.
- Anonymizing web browsing, with Tor Browser Bundle (we were using “development releases,” further down that page)
- Instant message OTR (“off the record” ) encryption, with Adium or Pidgin+pidgin-otr
- PGP email encryption, with Thunderbird & Enigmail
I won’t go over the install instructions here—there’s a repo for that, with download links and some instructions—but we guessed that this would be plenty to go over. (Especially PGP. I think anyone who’s set up and successfully used PGP can relate.)
Tor Browser Bundle was easy: download this program, install it, run it—it handles the nitty-gritty parts. It’s a testament to the progress the Tor Project has made in terms of making it easy—and therefore hard to screw up.
Adium/Pidgin went over fairly well. After installation, we walked people through setting up an account on jabber.ccc.de (as opposed to simply using a Google Talk account). We only had a couple minor hitches:
- The Pidgin installer (for Windows) doesn’t contain everything it needs and actually needs to download some things before going ahead with the install. It slowed things down a bit, but luckily the wifi and the download servers cooperated.
- We apparently overloaded the CCC chat server, by trying to register dozens of accounts all at once.
I think @mtigas just crashed http://t.co/AZBeDdy1Gj by having a room of 60 people create accounts!
— Al Shaw (@A_L) September 17, 2013
We moved on once it was apparent that we wouldn’t be able to get everyone hooked up with a working account — but most of the room had gotten it working and everyone seemed comfortable with the instruction.
PGP/GnuPG was obviously the toughest part, and we budgeted most of the installfest time for it. There are a lot of ways to do PGP encryption, but for simplicity’s sake we chose to standardize on Thunderbird & Enigmail because it works on all platforms and it provides a GUI for the entire PGP workflow.
We did run out of time—since we only had the space for a few hours—but by the end of it, many in the group were already able to find each others’ PGP keys and send each other encrypted e-mails.
What I Learned
- Audience, help thyself: I thought that I’d lost most of the group during the PGP portion of the installfest, but most people in the room were sitting next to someone who was able to keep up and also able to help out the people around them. This was a welcome surprise that I’d hoped for but tried not to rely on.
- Security is hard, focus really helped: It’s daunting to teach hard software to journalists across the whole range of technical backgrounds in just an hour and a half. So choosing very few easy or important tools was crucial—other talks and sessions I’ve been to simply throw lists of things at attendees, but our pared-down focus was essential to having people actually use these tools.
- Security is hard, but the tools are getting better: The thought of helping people set up PGP gives me the heebie jeebies. In the past, I’ve seen developers take over an hour to sort of kind of maybe have PGP keys and be able to send messages to each other…what hope do others have? But I jest. Thunderbird & Enigmail, while not the best pieces of software, have actually succeeded in making PGP possible (though still clunky) for people who are genuinely interested. Fact is, they can (mostly) get the job done today, even for people who aren’t crypto nuts.
Privacy, security, and surveillance issues aren’t just for nerds and spies anymore. Based on the post-Snowden interest I’ve seen in tools like Cryptocat and Tor and PGP, it looks like the open-source community is really starting to tackle the usability issues that used to plague this section of software. I’m looking forward to the next generation of tools to be even easier. (And I welcome any advance in usability that makes these tools more common and these workshops less necessary. In a perfect world and all that.)
Last Thoughts
The hybrid “talk + installfest” format was perfect for a topic like this. We fostered a conversation on why we were about to install the things (and why attendees should care), and then went about making it happen. The size of the group (about 70) made it not quite as hands-on as I would’ve preferred, but between Hacks/Hackers volunteers and some knowledgeable attendees in the room, the installfest was very successful.
I’m not an expert on cybersecurity and I avoid pretending that I am. But I’m immensely grateful to have a community of colleagues and other folks that I can tap into for advice and reality checks when I work on things like this. Massive kudos to Hacks/Hackers NYC for organizing and Meetup.com for providing a great space—I’ve never seen such graceful wifi at a large gathering involving laptops. And thanks to Jennifer Valentino-DeVries for providing context and advice, and also for helping out a little bit during the installfest.
I’m excited to have the opportunity to take this experience—my first time leading a training workshop—and continue to develop it and share. I offered to give some hands-on help to folks interested in crashing the weekly CSV Soundsystem meetup, and a handful of people took us up on the offer. I’ll be at the Online News Association conference (Oct. 17-19, Atlanta, GA), recording & assembling course material for my For Journalism class. And did you know that there’s an entire track dedicated to privacy issues at Mozilla Festival (Oct. 25-27, London, UK)? I’ll be facilitating some of the sessions there, too.
If you’re interested in getting in touch to chat about these issues or collaborate or bounce an idea, I’d love to hear from you.
Elsewhere:
- Our pre-installfest download instructions and some how-tos, on GitHub
- Justin Lancy collected live tweets from the @HacksHackersNYC account
- Columbia Journalism Review’s Behind the News blog
- Sean Connoly posted his notes from the event
Organizations
Credits
-
Mike Tigas
Developer, journalism troublemaker, internet troll. Knight-Mozilla @OpenNews Fellow at @ProPublica. Also: Onion Browser (Tor iOS), @TabulaPDF, @ForJournalism.