Features:
How to Lose Friends and Anger Journalists with PGP
Newsrooms have better options
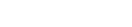
Simply untangle. (Esfema)
A few years ago I began sending hundreds of emails to strangers—many, encrypted.
I was launching into my graduate research on the security habits of investigative reporters, and I wanted to hear from journalists with a variety of backgrounds.
If I wanted to meet technologically savvy reporters, I learned that I could more reliably catch their interest by sending a PGP-encrypted email. I also learned that this is a great way to annoy, frustrate, or otherwise upset journalists.
To understand why, let’s talk about PGP, and why it’s often at odds with journalistic work.
What is PGP?
PGP stands for Pretty Good Privacy, an encryption standard created by Phil Zimmermann in the early 1990s. Zimmermann was a peace activist. For him, PGP was a way to allow grassroots political organizations to work without worry of government eavesdropping in the U.S. and abroad.
In 1991, the U.S. Senate debated an anti-crime bill poised to outlaw civilian access to strong encryption. Fearing that Congress would legislate away this right, Zimmermann says he worked to release his software online before such a law could pass.
At a time when strong encryption wasn’t available to the general public, PGP became one of the most powerful ways to secure messages and files.

A PGP encrypted message.
Just as your personal signature is difficult to imitate, PGP lets users create cryptographic signatures for files and messages, allowing other users to check their authenticity. Perhaps most importantly for journalists, PGP helps users encrypt messages and files.
Today, an open source implementation, GNU Privacy Guard, is the frontrunner used by technologists, the human rights community, and increasingly, journalists.
PGP in the Newsroom
For some reason, reporters have been getting very interested in secure communications.
In recent years, there has been an enormous spike in the apparent number of PGP users associated with newsrooms. Alongside other encrypted messengers such as Signal, WhatsApp, and others, it also seems like everyone with a secure tip page accepts PGP emails.
Though news organizations position PGP emails as a channel for sharing confidential tips, using PGP yields no more anonymity than an unencrypted email. If anonymity is the concern, look elsewhere.
So why do news organizations use it?
When I speak to journalists about why they got started with PGP, typically it’s not because they’re big crypto geeks. Reporters are always hustling for interesting tips and sources, and PGP can be part of the hustle. Like a lottery, the possibility of a payoff is a strong motivator.
Reporters get noise. In their voicemails, text messages, Facebook, Twitter, and email inboxes, they receive countless messages and tips that aren’t particularly newsworthy. That includes encrypted emails from graduate students soliciting interviews. But PGP doesn’t let you know you have noise until you spend the time to decrypt it.
PGP opens the door to new conversations, but often, it also makes real work harder than it needs to be, and that makes journalists angry.
So let’s pause and ask, what problem are we really trying to solve here?
Reporters want sources to feel comfortable reaching out, while also providing sufficient communication security. They also want useful information without sacrificing time or efficiency.
With very few exceptions, PGP is probably not the best channel for tackling these problems. Instead, it eats into the time reporters can spend elsewhere.
How PGP Gets in the Way
In an environment where a growing number of alternatives do the job faster, PGP comes with barriers for practical use in newsrooms.
The barriers typically fall into four categories. Using PGP requires (1) becoming painfully aware of cryptography, (2) routine maintenance, (3) vigilance to avoid security mistakes, and finally, these issues lead to (4) filtering who you can viably talk to.
Becoming Painfully Aware of Cryptography
Modern encrypted messengers (e.g., Signal, WhatsApp) don’t require much know-how. PGP is a little more “hands on,” requiring users to understand a brief primer in the basics of cryptography. These lessons apply to both PGP, as well as accessing the web over a secure connection.
Let’s begin this journey with a loose analogy for passing secure messages over the web.

(Soraya Okuda)
Janine and her friend, Ewen, want to exchange notes in class. They don’t sit near each other, so they rely on other students to help deliver their messages. To prevent the other students from reading their notes, they come up with a scheme.
To make the message unreadable to anyone else who helps them deliver their note, they could agree on a set of rules to scramble the message in advance (e.g., shifting letters by one; “A” becomes “B,” “B” becomes “C”), then use their rules to scramble and unscramble the message. Now the note, “Sixth grade is hard,” becomes “Tjyui hsbef jt ibse”—gibberish to anyone who doesn’t know the rules.

(Soraya Okuda)
This is a good start. But if other students in the class figure out the pattern to the scrambled message, they can also unscramble it themselves.
Still with me?

(Soraya Okuda)
Janine and Ewen could solve this problem using public key cryptography, the architecture behind PGP. This is also how we get secure connections to the web. In this arrangement, rather than simply shifting over the letters, Ewen and Janine have two sets of “keys,” both of which represent enormous numbers. They have a public key that they can share with anyone and scramble messages, and a private key can be used to unscramble the message.

If Janine and Ewen used PGP, the public and private keys would be represented by large blocks of text, generated and interpreted by the software. Their encryption scheme is so complex that only a computer could encrypt and decrypt the message. And without the private key, it would take an impractical level of computing power to unscramble the message.
Now if that sounds confusing, you’re in good company; even security professionals have a tough time explaining how this works.
By putting public keys front and center, PGP requires users to think about the mechanics of public key encryption, and puts responsibility for upkeep in the hands of users.
Routine Maintenance
If you want to encrypt a message to someone (e.g., tips@nytimes.com), you’d need to know where it’s going (e.g., their email) and their public key. Now you might wonder, where do you find a public key? How do you make sure it’s the right one? How do you use it now and in the future?
Welcome to the world of key management.
Many users share their keys using a key server—essentially an online phone book for public keys—such as the MIT key server. From there, you can search for the name, email address, or other information about whoever you want to reach out to.

If all goes well, your recipient has their current key on the key server.
… But a lot can go wrong. You may instead find that the key is expired. Maybe you’ve got the wrong email address. Or you may still accidentally encrypt to the wrong public key, or they may try to decrypt with the wrong private key. If they don’t get many PGP emails, they may have forgotten the password needed to unlock their private key. Or they might not have access to the device that has their private key, effectively making the email unreadable.
At least one of you will suffer an aneurysm.
Finally, you and your conversation partner will likely exchange unencrypted emails to troubleshoot these problems. If all goes well, you’ll finally send the email. And if not, you might also decide the exchange doesn’t need to be encrypted that badly.
Vigilance to Avoid Security Mistakes
We’ve talked about things that can go wrong that are simply inconvenient, but PGP is also a minefield for mistakes that can undermine security for journalists and their sources, demanding close attention.
As far back as 1999, researchers identified PGP usability challenges that make security slip-ups tough to avoid. According to more recent research, these issues largely persist. There are too many ways to slip up to name here, but let’s briefly canvas a few.
For new users, the distinction between a public and private key might not seem meaningful, but the private key is used to unscramble your messages and should not be shared.
So naturally, PGP makes it easy to share your private key.
Compare this to Signal. With every message sent the keys change, making it impossible for one key to decrypt all messages.
You could also simply encrypt to the wrong person. And key servers are great for impersonation. If you don’t have the right email and key, you might have an extraordinarily secure email exchange… with an impersonator.
In turn, the impersonator can also pretend to be you.
If an attacker manages to impersonate both you and your conversation partner, there’s nothing to stop them from forwarding your messages to the real recipient, effectively allowing them to sit in the middle of the conversation.
If reporters insist on using PGP, they need to authenticate, or ensure that they’re talking to the right person.
PGP allows users to authenticate using a shortened code that corresponds to the public key—a unique fingerprint.

Reporters and news orgs sometimes post fingerprints on webpages they control (e.g., the New York Times tip page). When importing someone’s key, users can compare their local fingerprint to their publicly posted fingerprint. If there’s a match, you’ve probably got the right key.
Users can also verify the legitimacy of a key by looking for other trustworthy actors who have cryptographically “signed” the key on a key server. Though in the real world, it’s very possible that no one has signed their key.
PGP is a Filter
Before you can speak to me over this channel, are you okay with a lesson in cryptography? How about key maintenance? How about tiptoeing through an unending minefield of security issues? Few people are willing to do all of these things.
For journalists, this means that a small sample of technologically inclined people will reach out this way. Journalists with unusually techy sources are the key beneficiaries.
Letting Go
Because of its architecture and design, even motivated users and security geeks have headaches with PGP. With a growing number of intelligent alternatives available (e.g., Signal), journalists should critically consider what problem they hope to solve, and adjust their tools and practices. Chances are, there’s an easier way forward.
In many ways, PGP is remarkable. It emerged to fill the void at a moment when powerful encryption was not available to the general public. But there’s no void now. Whenever possible, using simpler channels will make life easier.
Credits
-
 Martin Shelton
Martin Shelton
Dr. Martin Shelton is the principal researcher at Freedom of the Press Foundation, conducting user research on harassment of journalists and digital security education in J-schools.