Features:
Two-Factor Authentication for Newsrooms
The easiest ways to make it harder for attackers to access your accounts
Passwords are the brittle wall that keep unwanted visitors out of your accounts. Breaches can hit anyone, but as frequent targets with sensitive sources, work, and personal information at risk, reporters should take extra care. When it comes to account protection, two-factor authentication is one of the most effective defenses available.
Two-factor authentication (or 2FA, for short) strengthens login security by requiring a second piece of information—a second factor beyond your password. The second piece of information is usually a temporary code delivered by a device in your possession, such as your phone. It may also be something on your body, such as a fingerprint.
You might hear it referred to by a variety of names (e.g., multi-factor authentication, 2-step verification), but we’re going to stick with 2FA.
Why You Should Use 2FA
When large-scale password breaches happen—and they happen a lot—credentials are often sold and swapped in online marketplaces and hacking forums. Some attackers break into accounts for entertainment, and some, for a payday. It’s typically not personal. In rare circumstances, attackers have a specific group or person in their crosshairs.
Email accounts generally give attackers the most value. Why? You use your email to recover other web accounts.
Here are a few different ways your account is most likely to get hijacked.
Attackers will guess short or predictable passwords.
After a large-scale password breach, some attackers will use automated scripts to try logging in to multiple websites with the same hacked credentials, just in case you reuse passwords on multiple accounts.
Attackers will craft fake phishing pages to trick you into divulging your credentials. How? They’ll usually send an email that seems to come from a trusted source (e.g., Twitter), directing you to an ordinary-looking login page for a real site you trust, but the site is a bogus one under their control. This is why it’s important to look closely at the sender field, as well as the URL for the login page. You can learn more about phishing here.
Spear phishing is targeted phishing. Typically the attacker will do their homework, gathering publicly available information (e.g., social media, public records) to create a good pretext for the phishing email. They may impersonate a friend, colleague, or source, and direct you to a forged login page. This is how the Washington Post’s website got hijacked in 2013.
Each service has its own peculiarities that enable unique attacks, but these are common across most email services.
Journalists are radically public-facing people, and a big part of the job is clicking on links from strangers. Unfortunately, this means journalists are uniquely susceptible to phishing attacks.
Enable 2FA everywhere you can, but especially on your email. Check if your favorite service supports it on Twofactorauth.org, and look for step-by-step guides on TurnOn2FA.com. Let’s walk through a few ways to use it.
2FA Approaches
There are a few simple, widely supported approaches for adding 2FA to your accounts. There’s not one “right” way to use it, and each has unique considerations for security and convenience.
A Pretty Good Option: SMS Text Messages
When setting up 2FA, most services allow you to use regular old text messages. When logging in, you will receive a short confirmation code on your mobile device. When prompted during login, enter your code.

Text messages are a painless way to access 2FA codes, but are only as reliable as the phone network. For example, if you lose network access or travel outside the country, you might not be able to receive the messages.
There is no question that SMS-based 2FA is much better than using a password alone. But because telephone infrastructure itself comes with a great deal of baggage, SMS isn’t the most secure method available for targeted groups.
Here’s a great example. An attacker broke into the Twitter and email accounts of a prominent Black Lives Matter activist, Deray McKesson, by convincing Verizon to redirect his phone messages to a new SIM card on a remote device. This allowed the attacker to intercept his 2FA messages.
By calling @verizon and successfully changing my phone's SIM, the hacker bypassed two-factor verification which I have on all accounts.
— deray mckesson (@deray) June 10, 2016
That sounds scary, but remember the real story here: The attacker was forced to work much harder than if they had simply entered a password.
This is not likely to happen to most people, but journalists, remember that you’re worth it.
Compared to SMS messages, authenticator apps are a little more convenient, and a lot more secure.
Better Option: Authentication Apps
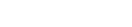
Some services allow you to receive your temporary login code from a mobile app. There are many options to choose from, such as Google Authenticator, Authy, Duo Mobile, and others.
Some web services let you attach multiple authentication apps to the same account, which can be incredibly helpful for getting login codes when multiple people need access. Authenticator apps are also great because they work when you don’t have access to your phone network (e.g., when traveling internationally).
Unlike SMS messages, authenticator apps can’t be intercepted on the phone network, making apps a hardened option.
Best Option: Security Keys
Right now, security keys are one of the most secure and efficient ways to use 2FA. A security key is a physical USB device you can use to authenticate into your account.
They’re pretty cheap—one of the most popular options, a Yubikey, will run you $18.
When prompted to provide your 2FA credentials, instead of typing in a code, you simply insert your security key and physically tap it when prompted during login. That’s all. Security keys are fairly resistant to phishing attacks, making them one of the best options available. Unlike code-based 2FA, phishing sites don’t have a great way to intercept information from security keys.
The main problem with Yubikeys is that as soon as you try one, you’ll want to use them everywhere. And they can’t be used everywhere yet.
Security keys are not yet as well supported as authenticator apps, but the standard is getting traction on large websites. It can be used to log into Google, Facebook, Dropbox, and other services.
Right now, using security keys to log into most websites requires browser support, and the Yubikey works with Opera and Google Chrome. (Full disclosure: I work with Google Chrome as a researcher.) Many other popular browsers are working to integrate support for Yubikeys and similar authentication devices.
Use whichever 2FA method is available and practical for you. SMS-based 2FA is a worthwhile upgrade, but when possible, consider using authentication apps or security keys.
Let’s Turn On 2FA!
We can set up 2FA in minutes. For example, let’s look at how to set it up for Gmail.
First, find the setup page.
Account icon (top right) > My Account > Sign-in & security > Signing in to Google > 2-Step Verification > Get started
First, you must register the device. Punch in your phone number. You’ll be sent a confirmation code on your mobile device, which you will enter on the registration page. If you prefer not to use your phone number, we can always remove it later.
After registering your device, you can use 2FA codes through SMS text messages.
Authenticator App
For a more secure way to use 2FA, let’s activate the authenticator app.
First, go to the application marketplace of your choice and download an authenticator app, such as Google Authenticator, Authy, or Duo Mobile.
On the 2-step verification page, scroll down to “Authenticator app” and click “Set up.” To register a new service in the app, you will be asked to scan a barcode that appears on your screen. After the code appears in your app, type the code into the setup prompt.
Security Keys
First, purchase a security key, such as a Yubikey. You can find one for $18 on Amazon.
They’re easy to set up!
Scroll down to “Security keys” and click “Add security key.” When prompted, insert the key into the USB port, and physically tap it.
Afterward, you can name your newly-registered device. During log in, instead of typing in a 2FA code, now you can just insert and tap the key.
If you already have authenticator apps or security keys set up, you probably don’t need SMS any more. If it’s not necessary, consider removing your phone number.
Scroll to “Voice or text message” and click the pencil icon, and then click “Remove phone.”
Some laptops (e.g., the 2016 Macbook) only have USB Type-C ports. If you can’t use a traditional USB 2.0 or 3.0 port, you can still use security keys with a USB Type-C adapter. Here’s a short list of Type-C adapters that are confirmed to work.
It’s a little more expensive to purchase Type-C Yubikeys.
Whenever You Can, Use Backup Codes
Even if we lose our security key and authenticator app, we can still avoid locking ourselves out by using backup codes. Scroll down to “Backup codes” and click “set up.”
You will see a series of numeric codes. Print these out, because if you are ever locked out of your account, you will need one of these codes to get back in. Keep these codes someplace where you can physically access them.

Team 2FA
So far we’ve only talked about situations where one person needs to log into an account, and they alone hold onto their authentication device.
But newsrooms often share login information, and chances are, more than one person has access to the Twitter account.
Do you need to ask for permission to use your colleague’s phone every time you want to log in?
Some services allow you to attach multiple apps or phone numbers to the account, while others don’t. For example, Google doesn’t permit users to register more than one authenticator app at a time, but does allow more than one phone number. By comparison, Twitter allows more than one app.
Get Started!
Does your favorite service offer 2FA? Drop by Twofactorauth.org to find out. You can also check out Turn It On for step-by-step guides on each service you want to secure. If your service doesn’t yet offer 2FA, consider prodding the organization to implement it, especially if the data entrusted to that service is sensitive and needs added protection.
Two-factor authentication will give you a strong edge over attackers, but don’t stop here. Learn more about how to defend your accounts against common attacks, and encourage your newsroom to do the same.
Credits
-
 Martin Shelton
Martin Shelton
Dr. Martin Shelton is the principal researcher at Freedom of the Press Foundation, conducting user research on harassment of journalists and digital security education in J-schools.